CNAME Cloaking: The Hidden Loophole in Third-Party Tracking
CNAME cloaking disguises third-party trackers as first-party, bypassing ad blockers and privacy measures. Learn how it works and its security risks.
Excerpt
Conversations about the death of third-party cookie usage have been persistent in the last few years. Apple has demonstrated progress in this area with Safari’s webkit utilizing Intelligent Tracking Prevention (ITP). In contrast, Google has taken the opposite action by indefinitely delaying its privacy sandbox for Chrome, ensuring a future for third-party trackers for now. This means advertisers, who rely on third-party cookies to track users and attribute ad performance, remain unaffected for now. However, as cookie deprecation looms, publishers are stepping up their efforts to mitigate the impact. Many are encouraging advertisers to adopt off-browser, server-side tracking or a newer approach involving changing the data collection party of on-browser tracking. This newer method feels somewhat nefarious in its attempt to circumvent third-party tracking restrictions and might surprise many with its feasibility. Below, I will explain how third-party tracking can become first-party, along with the security and privacy concerns associated with this approach.
First-Party (1P) vs Third-Party (3P)
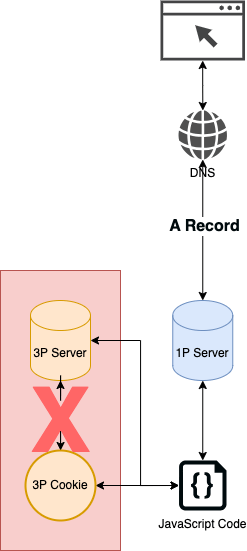
In web browsers, data collection through mediums such as session storage and cookies generally falls into two categories: first-party (1P) and third-party (3P) data. The key distinction between them lies in the ownership; first-party data is owned by the host server, while third-party is owned by an external server. Examples of third-party data include marketing and analytics platforms, which process information on a server separate from where the code is being run and data is being tracked.
Browsers were constructed with security permissions that regulate data access and availability based on ownership. This distinction allows browser companies like Google and Apple to implement policies that govern how data is stored and transported, depending on the type of ownership.
The DNS Workaround
Third-party entities cannot simply change their ownership to first-party through front-end code snippets (the common method by which third-party trackers gain access to data on a website). However, an increasing number of publishers are now asking advertisers to make a technical configuration within their server DNS records to make this happen. This approach marks a departure from simply browser-executed code to DNS alterations happening at the domain entry point.
Servers, IP Addresses, DNS, and CNAME
For those unfamiliar with how websites operate, a website is hosted on a server that is connected to the internet and accessible to anyone via a web browser or through an IP address. Similar to how home internet connections have IP addresses, every server has an IP address in either IPv4 (e.g., 192.142.1.1) or IPv6 (e.g., 2001:db8:3333:4444:5555:6666:7777:8888) format. Since these numeric addresses are not user-friendly, the Domain Name System (DNS) acts as the “phonebook of the internet”, allowing domain names to be mapped to IP addresses. DNS records come in various types (A, AAAA, CNAME, NS, and MX), but for this discussion, I will focus on CNAME records, which serve as the vehicle for converting third-party tracking into first-party.
CNAME
CNAME is short for canonical name, allowing one domain name to serve as an alias for another. Typically, A records are used for the parent domain (e.g., example.com), while CNAME records are used for sub-domains like blog.example.com or files.example.com. CNAMEs offer flexibility by allowing subdomains to be hosted on separate servers while operating under the parent domain’s authority. This structure can bypass browser security policies like Content Security Policy (CSP), which normally restrict external access to a parent domain, since CNAME records inherently authorize the connection.
Masquerading as First-Party
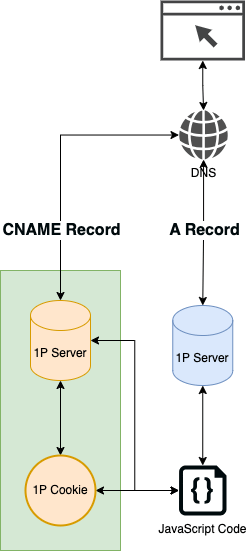
By creating a CNAME record that points to a third-party server, advertisers can deploy first-party cookies under the guise of the primary domain. The JavaScript libraries, cookies created, and server requests will appear as though they are coming from the first-party domain. This technique will allow the third-party companies to circumvent the deprecation of third-party cookies and evade services like ad blockers, which rely on blocklists of known tracking domains.
Security Concerns
When browsers make requests to a domain, they include all relevant cookies for that domain, often with minimal restrictions, unless SameSite attributes are explicitly configured. This can become a concern as browsers will automatically inherit all cookies for any subdomains of the domain name (e.g., virus.blog.example.com, backdoor.virus.blog.example.com for blog.example.com). Because of this, granting third-party access through a CNAME introduces several security risks:
- Session Highjacking & Data Exposure - Ability to gain access to authentication tokens, session storage, and sensitive user data.
- User Data Leakage - Login credentials and session information could unintentionally be shared with third-party entities.
- Expanded Attack Surface - If the server with CNAME access is compromised, attackers could inject malicious scripts or execute unauthorized actions on the site.
Privacy Concerns
This practice bypasses the user's awareness and consent, potentially violating trust and privacy laws such as GDPR and CCPA. Since users may not realize third-party tools are collecting data under the first-party disguise, they may unknowingly be subjected to extensive tracking. Additionally, you risk exposing the user to the security risks mentioned above.
What This Means for the Future
It should be no surprise that publishers, which depend on tracking and attribution for revenue, will continue to develop innovative ways to bypass privacy-focused prevention techniques. These techniques will persist long after third-party tracking is deprecated. In response, Webkit’s ITP has enhanced its CNAME cloaking detection by limiting cookie expiration for identified CNAME trackers to seven days. Given the ethical and legal gray areas surrounding this technique, it is crucial to understand the associated risks and ensure alignment with product, data governance, and legal teams before you decide what is best for you.